The address 203.160.175.158:14001 may look technical, but it represents a common concept used across the internet: an IP address combined with a port number. Whether you’re a developer, business owner, or curious user, understanding how such addresses work is essential for online safety, networking, and troubleshooting.
In today’s globally connected world, IP addresses and ports are the backbone of digital communication. However, they can also be linked to cybersecurity risks if misunderstood.
This guide explains everything you need to know—from basics to advanced safety practices.
What Does 203.160.175.158:14001 Represent?
- An address like 203.160.175.158:14001 consists of two parts:
- IP Address (203.160.175.158) → Identifies a device/server
- Port (14001) → Specifies a service or application
- Together, they help direct traffic to the correct destination.
| Component | Meaning | Example |
| IP Address | Unique device identifier | 203.160.175.158 |
| Port Number | Service channel | 14001 |
| Protocol | Communication rule | TCP/UDP |
| Usage | Web/app connection | Server access |
What Does 203.160.175.158:14001 Mean?
The IP Address (203.160.175.158)
An IP address identifies a device on a network.
- 203.160.175.158 is a public IPv4 address.
- It represents a server or device reachable over the internet.
- Anyone sending or receiving data from this device uses this IP as its unique locator.
The Port Number (14001)
A port works like a “door” through which a specific service on a server communicates.
14001 is a non-standard port.
Well-known ports like 80 (HTTP) or 443 (HTTPS) are not used here.
A custom port suggests:
- a specialized application
- a private dashboard
- an internal API
- a remote management tool
- or a data-collection endpoint
Combined Meaning
- 203.160.175.158:14001 points to a specific service running on that server, separate from standard web traffic.
How IP Addresses and Ports Work Globally
Every device connected to the internet has an IP address. Ports act like doors that allow specific types of traffic (web, email, apps) to enter or leave a system.
| Port Range | Type | Common Use |
| 0–1023 | Well-known | HTTP, HTTPS |
| 1024–49151 | Registered | Apps, services |
| 49152–65535 | Dynamic | Temporary connections |
QUICK POINTS
- IP = identity
- Port = communication channel
- Both are required for network communication
- Used globally in all internet systems
Resource Link:
Learn more about IP basics:
https://www.cloudflare.com/learning/network-layer/what-is-an-ip-address/
Why Do Servers Use Custom Ports Like 14001?
To Run Multiple Services on One Server
Different apps can run on the same IP by using different ports (e.g., port 80 for website, 14001 for an internal API).
For Internal or Private Tools
Organizations often host private dashboards, development tools, or admin consoles on high ports to keep them separate.
For Application Development & Testing
Developers use such ports when running Node.js/Java/Python apps, testing environments, or temporary services.
For Data Collection and Telemetry
IoT devices, monitoring tools, and log collectors often communicate through custom ports.
Common Uses of 203.160.175.158:14001
Such IP-port combinations are commonly used in:
| Use Case | Description |
| Web Applications | Hosting services |
| Remote Access | Server login |
| APIs | Data exchange |
| Gaming Servers | Multiplayer connections |
| IoT Devices | Smart systems |
What Type of Service Typically Runs on 203.160.175.158:14001?
While the exact application on this specific IP:Port cannot be identified without authorization, such ports often host:
Custom Web Dashboards
Admin UI, monitoring systems, or private company dashboards.
Data APIs
Apps that send or receive structured data via HTTP/TCP.
Remote Device Management
Tools for monitoring servers, CCTV controllers, or IoT networks.
Telemetry or Logging Services
Systems that collect logs, performance metrics, or device reports.
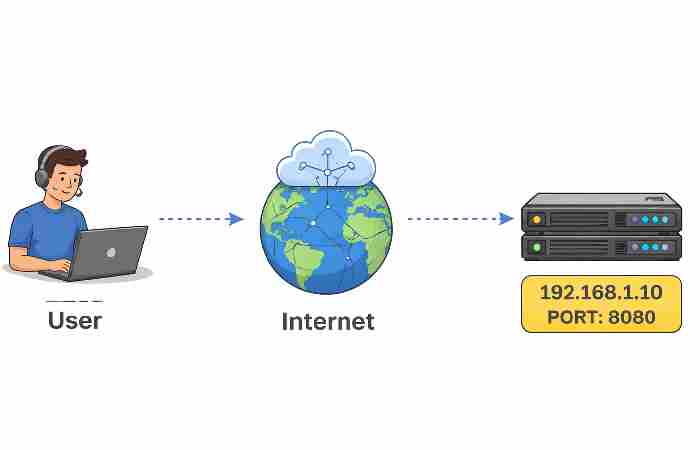
Visualizing How Data Travels Through Ports

When you access a service, your request travels through the internet and reaches the correct server using the IP and port combination.
| Step | Action |
| 1 | User sends request |
| 2 | DNS resolves IP |
| 3 | Port identifies service |
| 4 | Server responds |
| 5 | Data returns to user |
How Data Collection Works on an IP:Port Endpoint
If an endpoint like 203.160.175.158:14001 is configured for data collection, here’s how it typically functions:
Device or App Sends Data to the Port
Data may be pushed via:
- TCP
- UDP
- HTTP/HTTPS
- WebSockets
- Custom protocol
Server Listens on Port 14001
- A service binds to the port and waits for incoming data packets.
Data Is Processed and Stored
The server may:
- log the data
- store it in a database
- forward it to another system
- visualize it in a dashboard
- trigger alerts or automations
Authentication Controls Access
Authorized tokens, API keys, firewalls, or login systems ensure only approved devices connect.
Security Risks Associated with Unknown IP Addresses
Accessing unknown IP addresses like 203.160.175.158:14001 can pose risks.
| Risk | Explanation |
| Malware | Hidden harmful software |
| Phishing | Fake login pages |
| Data Theft | Personal info exposure |
| Unauthorized Access | System breaches |
Warning:
Never interact with unknown IP addresses unless you trust the source or understand the system.
Security Considerations for IP:Port Services
Using raw IP:Port combinations can expose services if not configured properly. Common risks:
Unauthorized Access
Attackers can scan for open ports and attempt intrusion.
Lack of Encryption
If the service doesn’t use HTTPS/TLS, data can be intercepted.
Weak Authentication
Hard-coded passwords or unprotected dashboards are major vulnerabilities.
Port Scanning Attacks
Automated bots frequently probe unusual ports like 14001.
Best Practices
- Use a firewall to restrict access
- Allow connection only from approved IPs
- Enable TLS/HTTPS where possible
- Use strong authentication
- Disable the port when not needed
- Monitor unusual activity
How to Check if an IP Address is Safe
Before accessing any IP, verify its legitimacy.
| Method | Tool |
| IP Lookup | WHOIS tools |
| Reputation Check | VirusTotal |
| DNS Check | Network tools |
| Reverse Lookup | Security platforms |
- Always verify unknown IPs
- Use trusted tools
- Avoid clicking random links
- Keep antivirus updated
How to Safely Access an Endpoint Like 203.160.175.158:14001
Only access this type of address if you have explicit permission.
Here’s the safe, standard approach:
Confirm What Service is Running
- Your admin/provider should tell you the protocol (HTTP/TCP/UDP/etc.).
Check Network Permissions
- Some networks block non-standard ports.
Use the Correct Access Tool
Examples:
- Browser (if it’s a web UI)
- API client (Postman, Curl)
- TCP client tools
- Device management software
Use Secure Login Credentials
- Never access without authentication.
Monitor and Log Connections
- Helps track misuse or unauthorized attempts.
Best Practices for Safe Internet Usage

| Practice | Benefit |
| Use VPN | Privacy protection |
| Enable Firewall | Blocks threats |
| Update Software | Fix vulnerabilities |
| Strong Passwords | Prevent hacking |
Why IP:Port Endpoints Are Still Popular in 2026
Even with cloud platforms and domain-based services, raw IP:Port endpoints are still widely used because:
They are easy to set up
Useful for development, testing, and internal systems.
They bypass complex hosting setups
Ideal for custom apps.
They offer direct communication
Perfect for IoT, sensors, and device networks.
They give full control
Admins can manage traffic, logs, and access rules.
Is 203.160.175.158:14001 Safe to Use or Access?
The safety of an IP like 203.160.175.158:14001 depends on its owner and purpose.
If it belongs to a trusted server, it may be safe. However, if unknown, it could be risky.
| Scenario | Safety Level |
| Trusted server | Safe |
| Unknown source | Risky |
| Suspicious activity | Dangerous |
Global Importance of Understanding IP and Port Security
Across industries—technology, finance, healthcare—understanding IP addresses is critical.
| Industry | Use |
| IT | Networking |
| Banking | Secure transactions |
| Healthcare | Data sharing |
| Education | Online systems |
Conclusion
Understanding 203.160.175.158:14001 helps you navigate the internet safely and efficiently. While IP addresses and ports are essential for communication, they also require caution.
By following best practices and verifying unknown sources, you can protect your data and ensure secure online interactions.

